The five phases of a ransomware attack
To choose the right antiransomware solution, you first need to understand the problem. Let us take a look at the five phases of a ransomware attack. Understanding each phase and being able to recognize the signs can help to defend your business against an attack effectively, or at least to lessen its effects. Do not forget that these attacks happen very quickly (around 15 minutes from infection to receiving the message demanding a ransom in return for data “recovery”). Hence the importance of a real-time protection system, like Mitra Antiransomware.
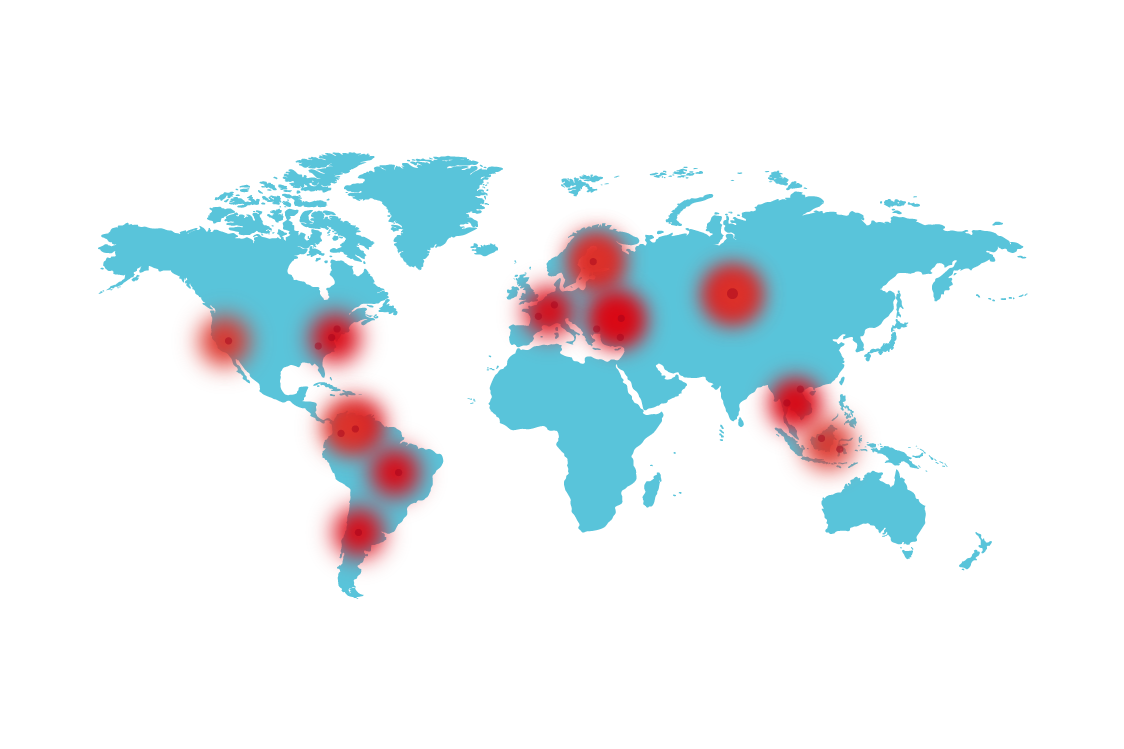
Fases_EN



